Dear Microsoft,
Hello. Today is Day-16 of our Active Directory Security School for you. Today, I will answer the question I had asked you on Day-15, and in doing so, we will learn about how to correctly audit who can change group memberships in Active Directory.
The Simple Trillion $ Question
Microsoft, in my previous post I had asked you a very simple Windows and Cyber Security 101 question, which was -
Who can modify the membership of a domain security group in Active Directory?
In case you're wondering why this might be an important question, as I've already explained, it is only so because today across 1000s of organizations worldwide, it is domain security groups that secure billions of organizational IT resources such as files, folders, email, data, SharePoint portals, Intranets, remote access etc. and thus they help protect trillions of dollars of wealth.
So, without further adieu, lets find out
what the answer is, shall we?! ...
First, the Incorrect Answer
Before I answer it, let me take a moment to share what the incorrect answer is, and the only reason I'm doing so is because in all likelihood, at 1000s of organizations worldwide today, this is exactly how IT personnel may be answering the question -
 |
| The Incorrect Answer |
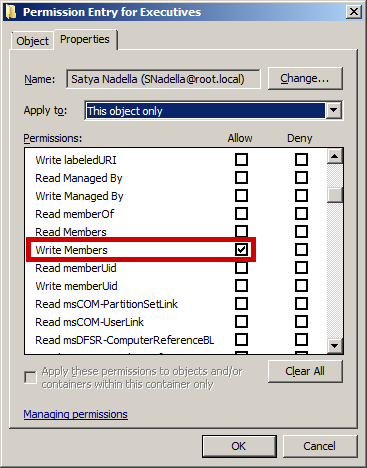
Find out / audit "who has Write-Property - Member (attribute) permissions on the security group."
Many will suggest that you can simply use tools like dsacls or acldiag, or simply write-up a PowerShell Script to do so, and most vendors will suggest using their Active Directory Permissions Audit tools. Sadly, and unbeknownst to them, they'd all be wrong!
If you've been attending school diligently, then you know why this is not only the incorrect way to audit who can change group memberships in Active Directory, but also that if you use this approach to do so, you're going to end up with vastly inaccurate results, acting upon which could leave thousands of IT resources inadequately protected and thus vulnerable to compromise.
Here's why...
Now, the Correct Answer
If you've been attending school diligently, then by now you know that it is not "who has what permissions in Active Directory" that matters, but rather "who has what effective permissions in Active Directory" that matters. In fact, that is all that matters.
Thus, the correct answer is -
Find out / audit "who has Write-Property - Member (attribute) effective permissions on the security group."
 |
Microsoft Effective Permissions Tab - Conceptually Correct Answer, But * Inaccurate and Inadequate
|
*Now, BEFORE you assume (and mistakenly and falsely so) that the Microsoft Effective Permissions Tab is sufficient to make this determination, please know that unfortunately not only is Microsoft's Effective Permissions Tab inaccurate, it is also substantially inadequate, as are all basic tools like dsacls, acldiag, PowerShell scripts etc. as explained in detail here and here.
I have already shared a substantial amount about Active Directory Effective Permissions, including why they are all that matters and why they are so difficult to accurately determine, which is also why the Effective Permissions Tab and virtually all other tools including dsacls, acldiag, PowerShell etc. just cannot be relied upon to accurately determine effective permissions.
To help organizational IT personnel worldwide understand this, let me share with you the only way that I know of, as former Microsoft Program Manager for Active Directory Security, to accurately audit effective permissions in Active Directory -
The snapshot above is that of the Gold Finger Active Directory Effective Permissions Calculator, which is the only tool that I know of that can correctly (i.e. accurately), automatically and adequately determine effective permissions in Active Directory.
As you can see above, we performed an Active Directory Effective Permissions Audit on a single domain security group called Executives, and we can see exactly who has Write Property - Member attribute effective permissions granted on this object.
I must mention that the only reason I have shared info about this tool here is to help everyone see exactly what it is they should be performing an audit of, and exactly what the output of such an audit looks like. You can download sample output from here.
I would encourage all organizations and IT personnel worldwide to compare the results of whatever method they might currently be using to make this vital determination on their domain security groups, with the results of a true effective permissions audit on their domain security groups. In all likelihood, in most cases the difference will be substantial, surprising and eye-opening.
Finally, Domain-Wide Assessment
Microsoft, there's an old saying that "Talk is Cheap." If I might add, "Actions are Not." If I were merely shedding light on this problem (as so many often do) without also doing something to help solve it, then I'd say the former saying would apply to me.
However, because I have the onus of representing the very best of not just Paramount Defenses, but also that of Microsoft (having been one of you), the onus of ensuring that I'm not just talking, is on me, so without further adieu, let me show you just how SIMPLE we have made the determination of such an important yet fundamental determination for the entire world.
If you can click a button, and I do literally mean just ONE button, you can now instantly, automatically and (most importantly) accurately find out exactly who can change the group membership of every single domain security group in an entire Active Directory domain, irrespective of whether it has 100 domain security groups or 100,000+ domain security groups -
 |
| Gold Finger - Active Directory Administrative (Privileged) Access and Delegation Audit Tool |
Imagine that an organization has thousands of domain security groups. Within minutes, this tool can accurately determine effective permissions/access on each one of these thousands of domain security groups to determine and reveal exactly who can change their memberships, AND how they can do so. (In contrast, it would several thousands of hours to do this manually.)
Microsoft, this quite simply is the state-of-the-art when it comes to true effective access entitlement assessment in Windows based networks, and this is what can empower organizations worldwide to instantly identify (audit), lock down, and then verify (and of course subsequently audit on demand 365-24-7) that on every single domain security group in their Active Directory domain, only those individuals who should actually be able to change group memberships (and no one else) can do so.
If you wish to see the complete output of the above domain-wide effective access assessment, you can download it from here.
At so many of our customers worldwide, there are thousands of domain security groups in their Active Directory domains. Within minutes, they can instantly and accurately find out exactly who can change the membership of each one of their thousands of domain security groups, as well as find out exactly how these individuals are entitled to do so, and within just days, they have been able to completely lock down (and maintain secure) access on every single domain security group in their Active Directory.
To say that this is an eye-opening experience for them, would be to substantially understate its profound value and impact.
Note: Microsoft, as you can imagine, in the wrong hands, the same power could be used to obtain and potentially misuse extremely valuable cyber security intel (e.g. exactly who can change the membership of Domain Admins, Enterprise Admins, Built-in Admins, Executives, Employees, Contractors, Project X Confidential Access Group, Litigation Y Access Group, Next Innovative Product Z Group etc. etc.) This is why we do not indiscriminately license this tool. In fact, we only license it to organizations and only for use within their own environments.
Something to Think About
Microsoft, in light of what I've just shared above, I'd like for you to give some serious thought to the following -
The need to know exactly who can change a domain security group in Active Directory is so basic, essential and fundamental to cyber security, yet even today, 17+ years after Active Directory was shipped, most organizations do not even seem to know how to do so correctly, let alone having the ability to do so correctly (, adequately, efficiently and on-demand.) Further, neither you, nor a single vendor (of which there are 1000s) in your global partner ecosystem have a single solution that can help the world fulfill this most basic, essential and fundamental cyber security need.
I can't help but wonder Why, and like I said, only one plausible explanation makes sense - this one (see "Here's Why" section.)
Summary
In summary, the primary objective of asking this simple question was to shed light on something that although may seem so very simple, is actually (not only) very important (but also very difficult to do correctly,) because it could possibly provide the easiest avenue for perpetrators to most easily compromise a substantially large number of organizational IT resources.
You see, in an Active Directory deployment, just about everything (i.e. all files, folders, email, SharePoint portals, applications, services, Intranet sites, remote access, Cloud access, Internet access, etc.) is ultimately protected by domain security groups.
Thus, if someone could change the membership of a domain security group in Active Directory, he/she could immediately obtain authorized access to every single organizational IT resource to which that domain security group is currently granted access.
This is why it is imperative to know exactly who can change the membership of all domain security groups in Active Directory.
The secondary objective was to help organizations worldwide understand that in order to correctly make this determination (i.e. to correctly find out who can change domain security groups in Active Directory), what they need to do is audit "who has what effective permissions" (i.e. this) and not "who has what permissions" on each single one of their domain security groups.
Finally, because "talk (alone) is cheap", I also wanted to share how easy we've made solving this problem for the entire world.
That's all for today.
Best wishes,
Sanjay
PS: Microsoft, I've some good news for you. Perhaps you may feel that I 've been a bit hard on you, but the good news is that Day-22 or so onwards, I'm going to show you and your customers just how rock-solid and trustworthy Active Directory is, how the world can easily attain and maintain least privileged access, and operate a bullet-proof Active Directory, so hang in there.




No comments:
Post a Comment